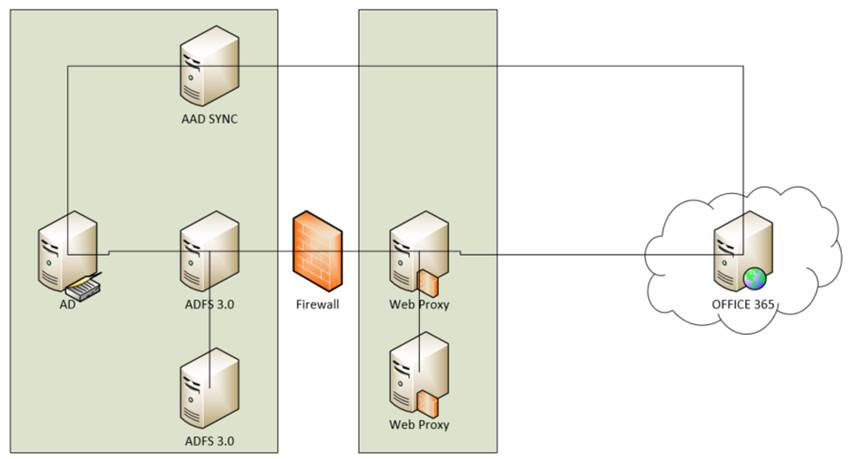
To get started with Office 365, this is a quick setup:
You will need:
- 3-5 servers, Windows Server 2012 R2
- AAD Sync, must be domain joined
- ADFS01, must be domain joined
- ADFS02, must be domain joined
- WebProxy01, should not be domain joined
- WebProxy02, should not be domain joined
- SSL certificate for federation gateway, e.g. fs.domain.com, it should be installed on all ADFS servers and Web Proxies.
- Access to all servers with installation account, which must be Domain Admin.
- Two AD service accounts, e.g. SVC-AADSYNC änd SVC-ADFS. Both have to be Domain User. AADSYNC will need more permissions for hybrid deployment: http://msdn.microsoft.com/en-us/library/azure/dn757602.aspx#BKMK_CreateAnADAccountForTheSyncService
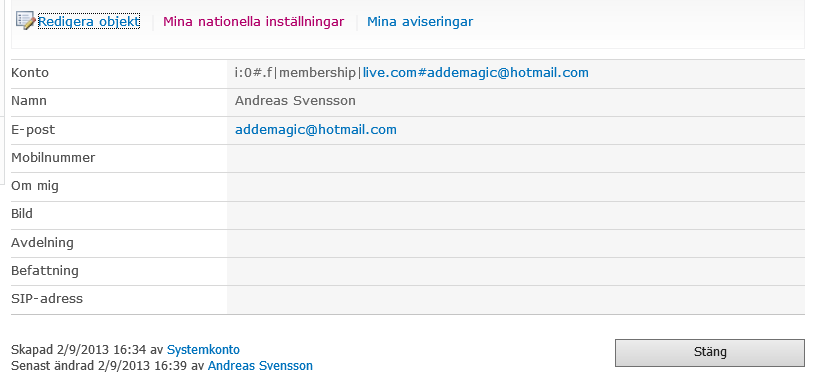
- Service account in Office 365 which is Global Administrator.
- Internal DNS for fs.domain.com pointing to ADFS-NLB.
- External DNS for fs.domain.com pointing to Web Proxy-NLB.
- Office 365 tenant with licenses for your users.
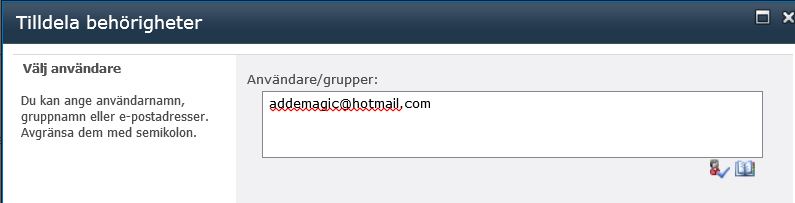
- Testaccounts!
Please document setup well. Happy clouding!